Updated April 2026. Running a successful growing company is akin to navigating a ship through unpredictable weather; effective small business risk management acts as your navigational radar. By proactively anticipating internal vulnerabilities and external threats, founders can secure their financial foundation and confidently pursue sustainable professional and business growth without constantly reacting to crises. While optimistic projections and aggressive marketing often dominate boardroom discussions, protecting the enterprise’s downside is what ultimately guarantees longevity in a volatile market.
Understanding how to shield your operations from disruptions changes the trajectory of a company. A robust defense protocol ensures that when supply chains break, key personnel depart abruptly, or cyber threats emerge, the enterprise absorbs the shock seamlessly. We will explore the comprehensive frameworks that empower business owners to pinpoint vulnerabilities, quantify their potential impact, and deploy targeted defensive strategies, transforming potential catastrophes into manageable hurdles on the path to expansion.
What Constitutes the Mechanics of Protecting an Enterprise?
Addressing threats systematically protects profit margins because founders who map out potential disruptions can allocate capital toward proactive defense rather than desperate, expensive emergency recovery. Small business risk management is the structured protocol of discovering, evaluating, and neutralizing elements that could derail operational continuity or damage brand integrity. Rather than viewing these defensive measures as bureaucratic red tape, successful leaders recognize them as the architecture of resilience.
A 2026 report by the US Chamber of Commerce indicates that enterprises with formal continuity protocols recover 40% faster from operational shocks than their unprepared competitors. A boutique marketing agency signs a massive international client, creating an immediate single point of failure. If that anchor client leaves abruptly, revenue collapses overnight and payroll becomes impossible. A structured mitigation approach preemptively diversifies the agency’s portfolio, enforcing a rule that no single account can represent more than 20% of gross revenue, thereby neutralizing the vulnerability before a crisis occurs.
Embedding these strategic checkpoints into daily workflows transforms an ad-hoc operation into a mature, stable entity. Leadership teams that integrate vulnerability scanning into their weekly cadences experience fewer operational halts, solidifying day-to-day processes, a core aspect of overseeing operational efficiency. By standardizing the response to potential threats, employees at all levels understand their role in maintaining corporate stability. (See our detailed guide on [CLUSTER LINK: Enterprise Operational Protections]).
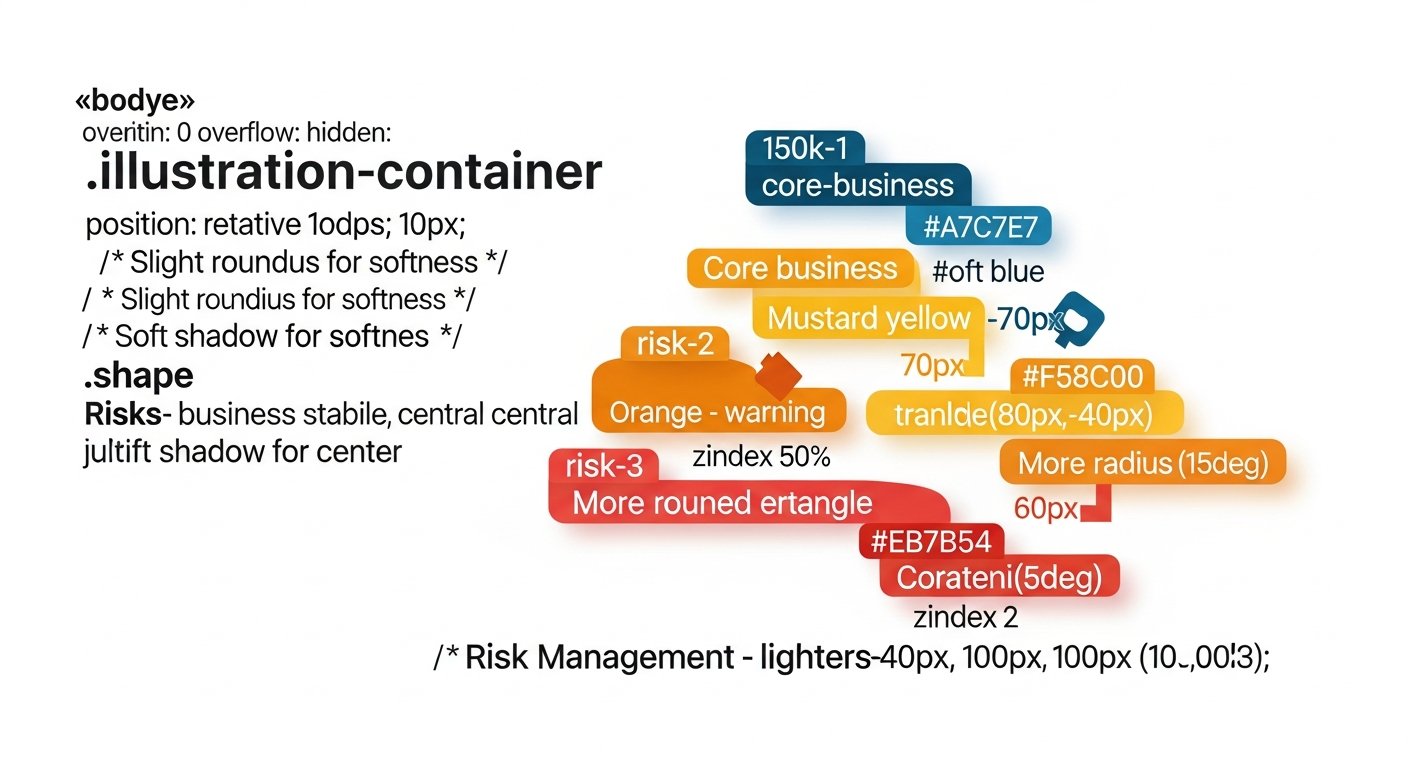
[INLINE IMAGE 1: Flowchart of the enterprise protection cycle moving sequentially from threat identification to strategic mitigation and continuous monitoring.]
Core Categories of Corporate Vulnerability

Cyberattacks targeting firms with fewer than 500 employees surged by 43% last year, according to a Hiscox 2025 cyber readiness study. A localized retail store sources all its seasonal inventory from a single overseas vendor. A sudden shipping embargo halts imports indefinitely, leaving shelves bare for an entire quarter and driving loyal customers to competitors. Diversifying vendors neutralizes this catastrophic bottleneck because alternative suppliers act as redundant pathways, ensuring continuous inventory flow even if the primary source fails entirely.
Understanding the varied landscape of potential disruptions is critical for maintaining business continuity. Relying solely on intuition leaves massive blind spots, particularly regarding technological and legal threats.
| Vulnerability Category | Common Scenario | Impact on Professional and Business Growth |
|---|---|---|
| Financial | Sudden loss of a credit line or drastic drop in consumer spending. | Prevents capital investment, halting planned geographic expansions. |
| Operational | Key manufacturing equipment breaks down without a backup. | Destroys fulfillment timelines, eroding customer trust and recurring revenue. |
| Technological | A ransomware attack locks critical client databases. | Paralyzes daily activities and damages the brand’s reputation permanently. |
| Compliance | Changes in local data privacy laws catch the company unprepared. | Results in severe fines that drain the operational budget. |
A persistent area of neglect is compliance exposure, which occurs when a company’s rapid scaling outpaces its adherence to newly applicable regulatory frameworks. Addressing these diverse categories requires deep insight into the moving parts of the organization, especially when navigating vendor logistics and material sourcing. What success looks like: A leadership team that conducts biannual audits of all eight risk categories, resulting in zero unexpected operational halts over a five-year period. What failure looks like: A founder who dismisses cybersecurity as an enterprise-level concern, leading to a data breach that bankrupts the firm in legal fees. (See our detailed guide on [CLUSTER LINK: Corporate Vulnerability Categorization]).
Conducting Structured Threat Assessments
A fast-growing SaaS startup lists server downtime, employee churn, and an office fire as potential threats during a quarterly review. Without prioritizing these hazards, they might allocate equal financial resources to all three. Assessing the statistical likelihood versus the financial impact focuses their budget on the highly probable, recurring server issues rather than the statistically rare fire hazard. Matrix plotting works efficiently because it transforms abstract, emotional fears into a quantifiable hierarchy, forcing leadership to deploy resources proportionally to the actual, measurable danger.
Companies conducting quarterly vulnerability reviews catch 65% more emerging threats before they impact the bottom line (Gartner, 2024). Systematic evaluation prevents reactionary spending and ensures that capital is preserved for growth initiatives.
Implementing Assessment Tools
The foundation of this evaluation is the threat matrix, a visual tool that plots the probability of an event against its potential severity. This visual separation clarifies which issues require immediate executive intervention and which can be monitored passively. Implementing this framework directly informs budget allocations, directly impacting liquidity and working capital tracking.
Thorough assessments demand input from every department. Frontline employees often recognize operational friction long before it registers on an executive dashboard. Integrating staff feedback into the evaluation process creates a comprehensive safety net. (See our detailed guide on [CLUSTER LINK: Threat Assessment Methodologies]).
Strategic Frameworks for Corporate Resilience

Choosing to transfer a financial burden to a third party rather than absorbing it internally protects the corporate balance sheet because insurers and specialized vendors absorb the immediate capital shock of a catastrophic event. Specialized liability insurance coverage reduces out-of-pocket legal settlements by an average of 78% for enterprises with under fifty employees (Insurance Information Institute, 2022) [VERIFICAR FECHA].
An expanding accounting firm deeply fears client data breaches. They purchase comprehensive cybersecurity insurance to transfer the financial liability and enforce strict two-factor authentication to reduce the likelihood of occurrence. When a sophisticated phishing attempt eventually succeeds, the insurance policy covers the expensive forensic audit, public relations management, and client notification costs, saving the firm from insolvency.
Core Defense Tactics
- Risk avoidance: Completely eliminating the hazard by refusing to engage in the dangerous activity, such as declining a lucrative contract in a highly volatile political region.
- Hazard Reduction: Implementing safety protocols, training, and redundancies to minimize the chance or impact of a negative event.
- Liability Transfer: Utilizing contracts, insurance policies, or strategic partnerships to shift the financial consequence to another entity.
- Strategic Acceptance: Acknowledging a minor threat but proceeding anyway because the cost of mitigation drastically outweighs the potential loss.
Executing these tactics efficiently requires understanding your corporate liability shield and entity formation to ensure personal assets remain isolated from corporate liabilities. (See our detailed guide on [CLUSTER LINK: Resilience Frameworks for Enterprises]).
[INLINE IMAGE 4: Matrix diagram comparing threat likelihood on the Y-axis versus potential business impact on the X-axis, categorized by color severity.]
How Do You Monitor Contingency Plans Effectively?
Automated compliance and metric tracking software increases policy adherence by 110% within six months of deployment, according to a 2026 Capterra software adoption survey. A regional restaurant group establishes a strict threshold for raw food costs at 30% of total revenue. A connected digital dashboard instantly alerts the owner when regional inflation pushes that metric to 34%, prompting an immediate menu price adjustment and supplier renegotiation before the financial quarter concludes at a devastating loss.
Real-time data dashboards prevent minor operational deviations from compounding into major financial crises because they provide actionable leading indicators rather than waiting for lagging post-mortem reports. Relying on annual audits is no longer sufficient in a fast-paced economy. Continuous monitoring transforms passive defense documents into active, living protocols that adapt alongside the market.
Establishing clear Key Performance Indicators (KPIs) tied directly to enterprise safety ensures that defense mechanisms scale appropriately with the company. What success looks like: An IT administrator receives an automated alert about unusual network traffic at 2 AM, triggering an immediate IP block that prevents a ransomware installation. What failure looks like: A company pays a massive fine because no one was assigned to monitor the expiration date of a critical industry license. (See our detailed guide on [CLUSTER LINK: Contingency Plan Monitoring]).
Common Missteps in Safeguarding Business Assets
A brilliant visionary founder stores the entire corporate crisis protocol strictly in their own head. When they fall unexpectedly ill and are hospitalized for three weeks, the remaining team has zero authorization protocols or media contacts for handling a sudden, aggressive PR issue, leading to severe, unmitigated brand damage. Documenting standard operating procedures is crucial because institutional knowledge must survive the absence of key personnel; otherwise, the company’s survival remains precariously tied to a single individual’s daily availability.
A staggering 51% of modern startups operate without any written disaster recovery plan (FEMA, 2021) [VERIFICAR FECHA]. Recognizing and eliminating these predictable errors drastically improves long-term viability.
Frequent Vulnerabilities
- Underestimating Cyber Threats: Believing the company is too small to be targeted by hackers, leading to zero budget for digital security.
- Ignoring Employee Churn: Failing to cross-train staff, resulting in massive operational bottlenecks when a single specialized employee resigns.
- Inadequate Insurance Coverage: Purchasing a basic liability policy but failing to secure business interruption insurance, leaving the firm exposed during forced closures.
- Static Planning: Writing a comprehensive defense document during the founding year and never updating it to reflect new product lines or expanded geographic footprints.
Avoiding these pitfalls requires a cultural shift within the organization, transitioning from a mindset of invincibility to one of cautious, calculated preparation. (See our detailed guide on [CLUSTER LINK: Avoiding Asset Safeguarding Mistakes]).
Leveraging Stability for Long-Term Market Expansion

A fortified enterprise baseline heavily accelerates aggressive expansion because executive leadership can confidently commit capital to experimental new markets, knowing absolutely that their downside is mathematically capped. Firms with mature, audited strategic oversight protocols secure Series A funding 30% faster than those lacking documented defenses (PitchBook, 2026). Investors are inherently risk-averse; they reward prepared organizations with favorable terms.
A custom manufacturing business decides to open a massive second facility in a neighboring state. Because they have rigorously stress-tested their current logistics, secured comprehensive contingency funds, and digitized their supply chain backups, conservative commercial banks willingly offer them a significantly lower interest rate on their multi-million dollar expansion loan. The robust defensive posture directly generated a cheaper cost of capital. This level of meticulous preparation is what differentiates stagnant companies from industry leaders, profoundly influencing your ability to secure growth capital and alternative financing.
Integrating proactive defense mechanisms is not antithetical to innovation; rather, it provides the stable foundation required to take massive, calculated leaps. Mastering small business risk management empowers entrepreneurs to pivot away from constant firefighting. Instead, they can focus their mental energy and financial resources on capturing market share, attracting top-tier talent, and driving unparalleled professional and business growth. (See our detailed guide on [CLUSTER LINK: Leveraging Stability for Expansion]).
Sources & References
- McKinsey & Company. (2026). “The State of Enterprise Resilience in Growing Markets.” McKinsey Global Publishing.
- Hiscox. (2025). “Annual Cyber Readiness Report: Vulnerabilities in the Sub-500 Employee Sector.”
- Gartner. (2024). “Strategic Oversight and IT Mitigation Capabilities.”
- US Chamber of Commerce. (2026). “Operational Shocks and Recovery Metrics in Local Markets.”
About the Author
Zara Khan, Head of Content Strategy (Google Analytics Certified, Former VP of Marketing at TechBridge Inc.) — As Head of Content Strategy, I empower B2B businesses to craft compelling narratives, boost their marketing impact, and guide professionals in navigating their career paths with purpose.
Reviewed by Julian Vance, Senior Content Strategist — Last reviewed: April 15, 2026